- Muneer Ahmad Dar
- Javed Parvez
Abstract—The increasing number of mobile operating systems that operates the small hand held devices called the Smartphone, has become integral part of our lives. The openness of these new environments has lead to new domain of apps and markets and has enabled greater integration with existing online services like e-banking etc. Smartphone makers are competing in turns to trump each other for storage, processor speed, platform compatibility and camera megapixels but it’s the largely software – the mobile OS – that makes the biggest difference to the popularity and market share of Smartphone. This paper evaluates the popular Smartphone Operating Systems with the purpose of understanding the user friendliness, popularity, user privacy and security and accessibility with the wide range of apps. Our research focused on the advantages and limitations of the Smartphone operating systems with the intension to find out if one of them has an edge on the other and finally we propose the enhancements so as to make them more user friendly and secure.
Keywords: mobile Operating Systems; Smartphone; Apps; Processor speed; Megapixels; Security; Accessibility.
- Introduction
Smartphone have become indispensible part of our life and everyone who uses it is getting addicted. Smartphone provides a wide variety of apps ranging from social networking to GPS based location searching that are useful for everyone in their day today tasks. In a study of 1,600 people including managers and professionals [1], Leslie Perlow, found that:
- 70% people said they check their Smartphone within an hour of getting up.
- 56% check their phone within an hour of going to sleep.
- 48% check over the weekend, including on Friday and Saturday nights.
- 51% check continuously during vacation.
- 44% said they would experience “a great deal of anxiety” if they lost their phone and couldn’t replace it for a week.
With these many professionals becoming dependent on Smartphone, which has necessary components of the computing platform: an operating system, applications and hardware. The main component of a Smartphone on which its functionality depends is the operating system ASmartphone,tablet or any other digitalmobile device is operated by the Operating system called the mobile OS. Modern mobile operating systems includes all the features of apersonal computeroperating system and in addition to that includes the features like atouch screen,cellular,Bluetooth,Wi-Fi,speech recognition,voice recorder, GPS mobile navigation,camera,video camera,music player etc.
The Smartphone operating system (OS) development has grown to include competitors such as Google, Microsoft, Apple, Symbian, and Palm with each of them trying to make it more user friendly and secure. Although these operating system platforms are trying their best and have come achieved a lot since their inception, none of these Smartphone companies provide a mobile OS that is ideal and satisfies all the users in terms of user friendliness and privacy. They claim that their platforms perform the best in all situations and will certainly not advertise any weakness with their Operating systems. This makes it difficult for end users particularly to a novice user to know which platform is best suited for their need.
Get Help With Your Essay
If you need assistance with writing your essay, our professional essay writing service is here to help!
In this paper, we perform a comprehensive analysis of each mobile operating system in order to identify the strengths of one Operating System over other operating system. Section II gives the overview of various Smartphone operating systems. In section III we identify the limitations of mobile operating systems. In section IV we propose the enhancements which could be implemented in the Smartphone Operating Systems and finally we draw our conclusions in section V.
- Smartphone Operating Systems
- ANDROID
Andy Rubin, Google’s director of mobile platforms, commented “There should be nothing that users can access on their desktop that they can’t access on their cell phone.” [1]. with this vision the popularity of smart phones having Google’s Android Operating System is continuously on the rise in the 21st century.
.Android is a comprehensive operating environment based on Linux kernel, it is also a layered system; the architecture of Android system is shown as in picture [3]. Applications layer is the site of all Android applications including an email client, SMS program, maps, browser, contacts, and others. All applications are written using the Java programming language. Application framework layer defined the Android application framework. All Android applications are based on the application framework. The Android application framework including:
- A rich and extensible set of Views that can be used to build an application with beautiful user interface, including lists, grids, text boxes, buttons, and even an embeddable web browser.
- A set of Content Providers that enable applications to access data from other applications (such as Contacts), or to share their own data.
- A Resource Manager that provides access to non code resources such as localized strings, graphics, and layout files
- A Notification Manager that enables all applications to display custom alerts in the status bar.
- An Activity Manager that manages the lifecycle of applications and provides a common navigation back stack.[1].

Figure 1: Android System Architecture [3]
Some of the advantages of Android over other Smartphone operating systems is listed as under.
- The ability to run tens of thousands of apps just like the iPhone but with choice of phone models that you can choose from. The choice of with or without physical keyboard, shape, color, phone size, screen size, manufacturer, features, and phone carrier. No more monopoly by one company on one carrier.
- Android allow developers/programmers to develop apps (applications) in what is known as “application without borders”.
- Android is beginner friendly and supremely customizable the more you use Google’s services, the more Android will shine Android has the majority of the market and the user experience is improving quickly.
- Google’s Android Now checks your location and calendar to automatically show you relevant info e.g. traffic to work, cafes, and flight details and lets you search with natural voice commands and replies with natural speech.
- Android is an open source service. This means that it’s free and anyone can use it. Anyone can modify and improve the software making it more effective and personalized. Applications are freely made and designed for Android by numerous app developers all over the world and these apps are offered for free on the Android market place. This feature of open source has also attracted mobile phone producers to manufacture phones using Android OS
- Android is not just an operating system designed for individuals but it also fulfills your business needs at the same time. Android market place offers numerous apps that are specially designed to manage your business. Now you can have a closer look at your business processes on the go with the help of these apps.
- IPHONE OS
iOS is the mobile operating system developed by Apple Inc. It is the second most commonly used operating system behind Google’s Android. Unlike Android it can be installed only on Apple’s hardware.
The iPhone OS has seen a rapid rise in popularity and garnered a large and dedicated user base. The iPhone OS has risen so far and so fast primarily due to the innovations on user interface and availability of 3rd party applications [11].
Unlike the Android security architecture, iOS security model provides different philosophy for achieving mobile device security and user’s protection. The iOS application platform empowers developers to create new applications and to contribute to the application store. However, each application submitted by a third party developer is sent to the revision process. During the revision process the application code is analyzed by professional developers who make sure that the application is safe before it is released the application store. However, such an application, when installed, gets all the permissions on a mobile device. Application might access local camera, 3G/4G, Wi-Fi or GPS module without user’s knowledge. While Android lets each user handle its own security on their own responsibility, the iOS platform makes developers to write safe code using iOS secure APIs and prevents malicious applications from getting into the app store. The iOS security APIs are located in the Core Services layer of the operating system and are based on services in the Core OS (kernel) layer of the operating system [14]. Application that needs to execute a network task, may use secure networking functions through the API called CFNetwork , located in the Core Services layer. The iOS security implementation includes a daemon called the Security Server that implements several security protocols. The Security Server has no API with public access. Instead, applications use the Keychain Services API, the Certificate, Key, and Trust services API, which in turn gets access with the Security Server.
- SYMBIAN
The Symbian OS was designed specifically for mobile devices with its small memory footprint and consumes low power. It is an open OS, enabling third party developers to write and install applications independently from the device manufacturers. An extensive C++ API is provided which allows access to services such as telephony and messaging, in addition to basic OS functionality. The Symbian OS was designed so applications could run for years without losing the user data. Also the OS has the capability of being platform independent and can run on more than one hardware platform [6, 7, 8, 9].
- WINDOWS MOBILE
This platform is based on Windows CE (WinCE). WinCe is a compact OS specifically designed for pervasive devices. It is focused on providing a consistent interface for applications on various hardware platforms which emphasizes portability by providing the user with the Win32 API. The hardware platforms include Packet PCs, Smartphone, Portable Media Centers, and even onboard computers in automobiles. The Windows Mobile platform was designed for flexibility and with the developer in mind. For that reason it was designed to support lots of preemptive multitasking. It supports a whopping 256 priority levels for threads and up to 32 processes. It supports all of the standard mutual exclusion and synchronization methods you would expect from a desktop PC. This functionality makes it ideal for a Smartphone because the users typically demand multitasking and want to be as productive as possible [4, 7, 8, 9 ].
- PALM OS
Palm OS is a proprietary operating system originally developed by Palm Inc. In the early versions (preâ€Garnet), the Palm OS was primarily utilized in Palmâ€developed Personal Digital Assistant (PDA) mobile hardware units. At one point, Palm PDAs with the Palm OS held 85% of the market share in the mobile device market [12]. However, in recent years, Palm’s market share has been in decline, mostly due to the stagnant nature of the OS development and has yielded the leading position to Symbian [6, 7, 8, 12].
- Limitations of Mobile Os
As discussed in the previous sections, the mobile operating systems are competing for the major market share and are claiming to be the best for the users, yet they have number of limitations in their platforms which for obvious reasons they are not disclosing to their users. The malicious apps aimed at mobile devices have risen from about 14,000 to 40,000 in less than a year. This rise in the malicious apps requires the strong OS. The limitations of the Mobile operating systems are listed as under:
- All or No Permission: A user cannot grant single permissions, while rejecting others in order to install the app. Among the list of permissions an app might request a suspicious permission among the other legitimate permissions, will still be able to confirm the installation.
- Mobile devices may download malware which the mobile OS is not able to trace. The novice users may download apps that contain malware unknowingly because it can be disguised as a well known game, security patch by OS, utility, or other useful application. It is difficult for users to tell the difference between a legitimate app and one containing malware.
- Often, the users of the app cannot judge the appropriateness and legitimacy of permissions for the app in question. In some cases it may be well understood, for example when a chess game app requests the privilege to reboot the Smartphone or to send SMS messages. In many cases, however, users will simply not be able to understand the appropriateness of the permission.
- Functionality, which is supposed to be possible only given the appropriate permissions, can still be achieved with less number of permissions or even with none at all.
- In case of the iOS , the user is not at all informed about any of the permissions. The app can access any of the resources without the permission of the user.
|
Resistance against |
Google Android |
Apple iOS |
|
Malware Attacks |
25% |
100% |
|
Web Based attacks |
100% |
100% |
|
Social Engineering Attacks |
0% |
0% |
|
Resource/Service Attacks |
50% |
75% |
|
Data Loss |
25% |
50% |
|
Data Integrity Attacks |
25% |
50% |
- Resistance of Android and iOS against various attacks.
- Proposed OS Enhancements
In order to enhance the security of the mobile operating systems we propose the following Enhancements:
- Need Based Permission System (NBS): The Need-Based Security (NBS) system designed to enhance the privacy of the user at run time. The main advantage of the proposed NBS system is that the user is informed about the authorized and unauthorized access of the resources at run time. The NBS system can be implemented in the operating system to provide the permissions at run time. Currently the Os is either including all the permissions without the information of the user as in case of iOS or it forces the user to accept all the permissions at install time as in case of the worlds popular OS Android. The most important file AndroidManifest.xml which lists the permissions of the app can be modified at run time by providing the need based permission system whenever the app is asking for the permission the user may be informed at that moment. For example, let us examine the Dial Kashmir app available on Google Play which gives all the details of Tourist places in Kashmir and contact details of important places like universities, government offices etc. The main permission this app may require is the INTERNET. If it includes MANAGE_ACCOUNTS which is the permission that allows the app to retrieve the user account information from the phone, our operating system will get the permission from the user at run time to access the resource and if user allows then only the permission will be granted. The main advantage of our NBS system is that it gives freedom to the users and the programmers to write a code which does not result in usability issues. Need based permission system and getting permission approvals at run time is a relatively new but promising approach as it gives lot of freedom to the novice users.
- Security API: In order to deal with the malicious apps downloaded by the user, we propose a security API which can be integrated with the existing security framework of mobile operating system. The objective is to provide security against the Apps which are installed by the end user and is given all the permissions at the time of installation. This enhanced security has the desirable property of not disturbing a regular user in any noticeable way. In fact, the user need not even be aware that the Security API has been applied. We have to prevent the modification and access of data from mobile phones by other external malicious applications unknowingly. We propose an API which will enhance the security of existing Android Framework.
The first step in our proposed security API is implemented by adapting an encryption technique utilizing Advanced Encryption Algorithm (AES) and applying it to all the personal files in the Smartphone. File operations offered by the proposed Security API should aid in the detection of potentially malicious Apps whose behavior matches that of Malware. Malware recognition is usually achieved by signature matching, heuristic analysis, or comparing hash-values
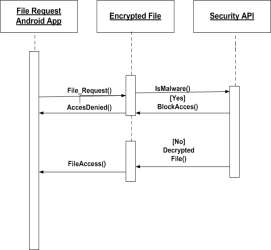
Fig 4: Sequence Diagram of the System
- Conclusion
The increasing trend of Smartphone usage by individuals of all ages has brought forward stiff competition between different Smartphone OS’s and Google’s Android OS. However, recent researches and reports revealed that the novice users are not secure on these platforms because of the limitations of these OS. We found different types of limitations in various mobile Os and particularly in Android and iOS which are the leading mobile Operating Systems. We found that there is a major need of modification in the permission based model of security system and we strongly recommended the implementation of Need based security system in the mobile operating systems so that the novice user can be informed at run time about the access to its various resources.
References
- Perlow, L.A.: Sleeping with your smartphone:how to break the 24-7 habbit and change the way you work, Harvard Business review press, 2012.
- Kataria, A.; Anjali, T.; Venkat, R., “Quantifying smartphone vulnerabilities,”Signal Processing and Integrated Networks (SPIN), 2014 International Conference on, vol., no., pp.645,649, 20-21 Feb. 2014doi: 10.1109/SPIN.2014.
- Bornstein, Dan. 2008. “Dalvik VM Internals”. http://sites.google.com/site/io/dalvikâ€vmâ€internals>
- Delac, G.; Silic, M.; Krolo, J., “Emerging security threats for mobile platforms,”MIPRO, 2011 Proceedings of the 34th International Convention, vol., no., pp.1468,1473, 23-27 May 2011
- Muneer Ahmad Dar and Javed Parvez.: “A Novel Strategy to Enhance the Android Security Framework”.International Journal of Computer Applications91(8):37-41, April 2014. Published by Foundation of Computer Science, New York, USA.
- Cleron, Mike. “Androidology †Part 2 of 3 †Architecture Overview.” 11 November, 2007.
<http://www.youtube.com/watch?v=fL6gSd4ugSI>
- Cleron, Mike. “Androidology †Part 3 of 3 †Architecture Overview.” 11 November, 2007.
<http://www.youtube.com/watch?v=MPukbH6Dâ€lY> .
- [8] DeviceForge.com. 2006. “Sun blesses Java phone”.
<http://www.deviceforge.com/news/NS6109398413.html> (accessed 14 April 2009).
- Dilger, Daniel E. “iPhone 2.0 SDK: The No Multitasking Myth.” 13 March 2008. Roughly Drafted Magazine. <http://www.roughlydrafted.com/2008/03/13/iphoneâ€20 sdkâ€theâ€noâ€multitaskingâ€myth/> (accessed 8
February 2009).
- Dilger, Daniel E. “iPhone OS X Architecture: the Mach Kernel and RAM.” 13 July 2007. Roughly Drafted
- Magazine. <http://www.roughlydrafted.com/2007/07/13/iphoneâ€osâ€xâ€architectureâ€theâ€machâ€kernelâ€andram/>
- Faas, Ryan and David Haskin. “Review: Which smart phone OS works best?”.
http://www.computerworld.com/action/article.do?command=viewArticleBasic&articleId=9117021
[14]. Apple inc., iOS Reference Library, Security Overview, http://developer.apple.com/library/ios/#documentation/Security/Conceptual/Security_Overview/Introduction/Introduction.html#//apple_ref/doc/uid/TP30000976-CH201-TPXREF101
Cite This Work
To export a reference to this article please select a referencing style below: